In today's digital age, the handling of sensitive information is more critical than ever. Two terms that often come up in discussions about data protection are PII and PHI. Understanding the differences between Personally Identifiable Information (PII) and Protected Health Information (PHI) is essential for organizations that deal with personal and health data. This blog post will delve into the definitions, examples, regulations, and best practices for managing PII and PHI.
Understanding PII and PHI
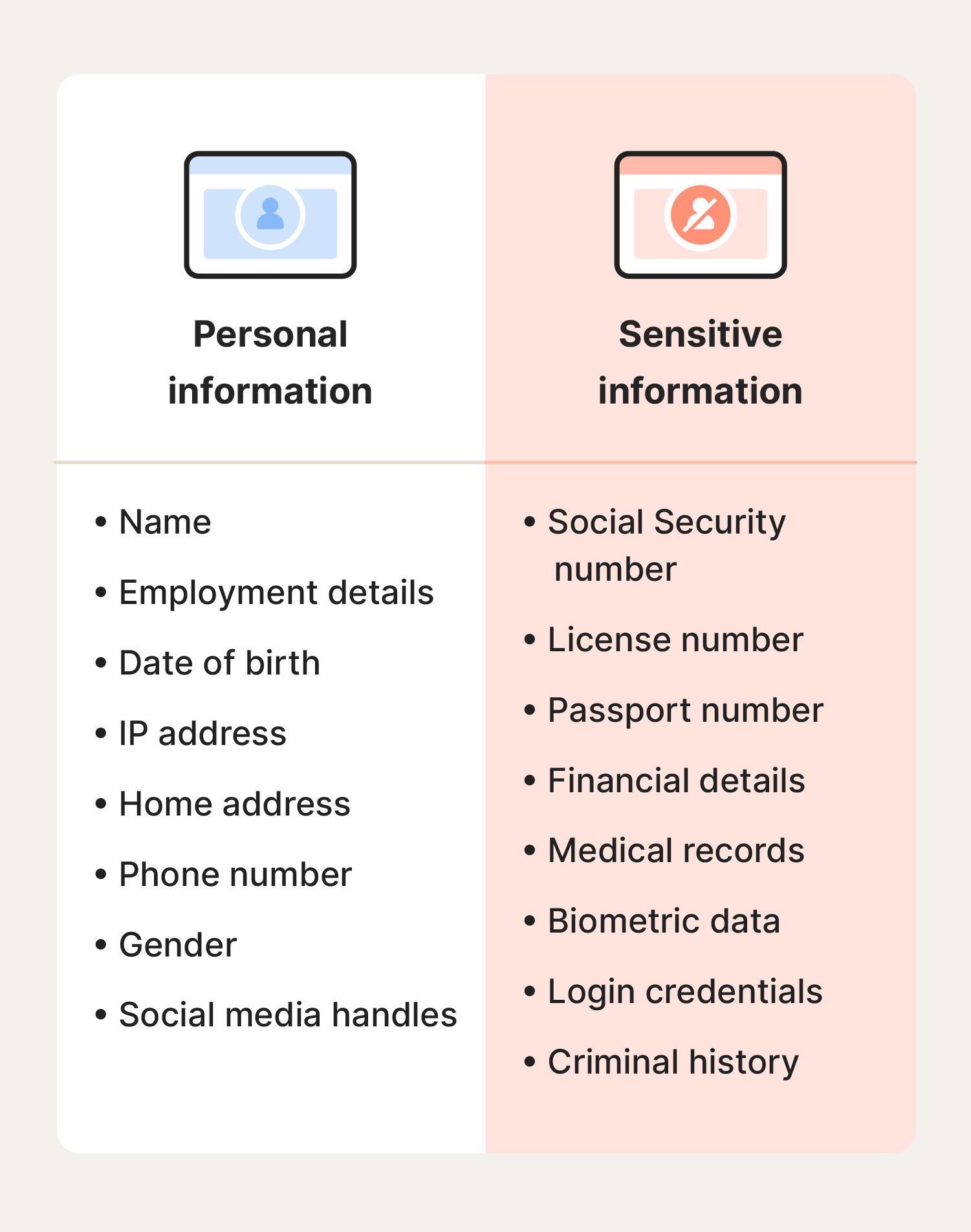
Personally Identifiable Information (PII) refers to any data that can be used to identify a specific individual. This includes a wide range of information, from names and addresses to social security numbers and biometric data. PII is crucial for various applications, such as customer service, marketing, and identity verification. However, it also poses significant risks if mishandled, as it can be used for identity theft and other malicious activities.
Protected Health Information (PHI), on the other hand, is a subset of PII that specifically relates to an individual's health status, provision of healthcare, or payment for healthcare. PHI includes medical records, health insurance information, and any other data that can be linked to an individual's health. The handling of PHI is governed by stringent regulations to ensure the privacy and security of sensitive health information.
Examples of PII and PHI
To better understand PII and PHI, let's look at some examples of each:
Examples of PII:
- Full name
- Home address
- Email address
- Phone number
- Social Security number
- Driver's license number
- Passport number
- Biometric data (fingerprints, facial recognition)
Examples of PHI:
- Medical records
- Health insurance information
- Diagnosis and treatment information
- Prescription information
- Medical test results
- Healthcare provider information
- Any data that can be linked to an individual's health status
Regulations Governing PII and PHI
Both PII and PHI are subject to various regulations designed to protect individuals' privacy and security. Understanding these regulations is crucial for organizations that handle such data.
Regulations for PII
Several laws and regulations govern the handling of PII, including:
- General Data Protection Regulation (GDPR): A comprehensive data protection law in the European Union that applies to any organization processing the personal data of EU citizens.
- California Consumer Privacy Act (CCPA): A state law in California that provides consumers with rights over their personal data, including the right to know what data is collected and the right to delete it.
- Health Insurance Portability and Accountability Act (HIPAA): While primarily focused on PHI, HIPAA also covers PII related to health information.
Regulations for PHI
PHI is governed by specific regulations, the most notable being:
- Health Insurance Portability and Accountability Act (HIPAA): This federal law in the United States sets standards for the protection of PHI. It includes provisions for data privacy, security, and breach notification.
- Health Information Technology for Economic and Clinical Health (HITECH) Act: This act enhances the privacy and security provisions of HIPAA and provides for increased enforcement and penalties for non-compliance.
Best Practices for Managing PII and PHI
Managing PII and PHI requires a comprehensive approach that includes technical, administrative, and physical safeguards. Here are some best practices for handling these types of data:
Data Minimization
Only collect and store the minimum amount of PII and PHI necessary for your operations. This reduces the risk of data breaches and ensures compliance with regulations.
Encryption
Encrypt PII and PHI both at rest and in transit to protect it from unauthorized access. Use strong encryption algorithms and regularly update encryption keys.
Access Controls
Implement strict access controls to ensure that only authorized personnel can access PII and PHI. Use role-based access controls (RBAC) and multi-factor authentication (MFA) to enhance security.
Regular Audits and Monitoring
Conduct regular audits and monitoring of your data handling practices to identify and address potential vulnerabilities. Use intrusion detection systems (IDS) and intrusion prevention systems (IPS) to monitor for suspicious activity.
Employee Training
Provide regular training to employees on the importance of data protection and the specific regulations governing PII and PHI. Ensure that all staff members understand their roles and responsibilities in protecting sensitive information.
Incident Response Plan
Develop and maintain an incident response plan to quickly and effectively respond to data breaches or other security incidents. This plan should include steps for containment, eradication, and recovery, as well as notification procedures for affected individuals and regulatory authorities.
🔒 Note: Regularly review and update your incident response plan to ensure it remains effective and compliant with current regulations.
Challenges in Managing PII and PHI
Despite the best efforts, managing PII and PHI presents several challenges. Some of the key challenges include:
- Data Breaches: The risk of data breaches is ever-present, and organizations must be vigilant in protecting against both internal and external threats.
- Compliance Complexity: Navigating the complex web of regulations governing PII and PHI can be challenging, especially for organizations operating in multiple jurisdictions.
- Technological Advancements: Rapid technological advancements, such as the rise of cloud computing and the Internet of Things (IoT), present new challenges and opportunities for data protection.
- Human Error: Human error remains a significant risk factor in data protection. Employees may inadvertently disclose sensitive information or fall victim to phishing attacks.
Case Studies: Lessons Learned from Data Breaches
Learning from past data breaches can provide valuable insights into the importance of protecting PII and PHI. Here are a few notable case studies:
Equifax Data Breach
In 2017, Equifax, one of the largest credit reporting agencies in the United States, experienced a massive data breach that exposed the PII of approximately 147 million people. The breach highlighted the importance of timely patching and vulnerability management. Equifax failed to patch a known vulnerability in its systems, allowing hackers to gain access to sensitive data.
Anthem Data Breach
In 2015, Anthem, one of the largest health insurance companies in the United States, suffered a data breach that compromised the PHI of nearly 80 million individuals. The breach underscored the need for robust security measures and incident response plans. Anthem's failure to detect and respond to the breach in a timely manner resulted in significant financial and reputational damage.
Uber Data Breach
In 2016, Uber experienced a data breach that exposed the PII of 57 million users and drivers. The breach was particularly concerning because Uber attempted to cover it up and paid hackers to delete the data. This case highlights the importance of transparency and ethical behavior in data protection. Uber's actions not only violated regulations but also eroded public trust in the company.
Future Trends in PII and PHI Protection
As technology continues to evolve, so do the methods for protecting PII and PHI. Some emerging trends in data protection include:
- Artificial Intelligence and Machine Learning: AI and ML can be used to detect anomalies and potential threats in real-time, enhancing the ability to prevent data breaches.
- Blockchain Technology: Blockchain can provide a secure and transparent way to manage and share PII and PHI, ensuring data integrity and privacy.
- Zero Trust Architecture: This security model assumes that threats can exist both inside and outside the network, requiring continuous verification and authentication.
- Privacy-Enhancing Technologies: Technologies such as differential privacy and homomorphic encryption can protect data while allowing for useful analysis and processing.
These trends offer promising avenues for enhancing the protection of PII and PHI, but they also present new challenges and considerations. Organizations must stay informed about emerging technologies and adapt their data protection strategies accordingly.
In conclusion, understanding and managing PII and PHI is crucial for organizations that handle sensitive information. By adhering to regulations, implementing best practices, and staying informed about emerging trends, organizations can protect the privacy and security of individuals’ data. The challenges are significant, but with the right approach, it is possible to mitigate risks and build trust with customers and stakeholders. The future of data protection will continue to evolve, driven by technological advancements and the ever-changing landscape of cyber threats. Organizations must remain vigilant and adaptable to ensure the ongoing protection of PII and PHI.
Related Terms:
- phi vs pii chart
- pii and phi examples
- pii and phi identifier
- pii and phi data
- pii and phi acronyms
- pii and phi difference